Virus Protection, Scan, Removal. Best Antivirus Protection for Computer and Mobile Device
-
Remove Win32/Sality.AT
2(9)0(0)There are different types of computer virus, but this type can be considered the most dangerous computer virus. Win32/Sality.AT is a malware which deletes everything it finds, by turning it into a shortcut file. It infects everything, even files stored on USB or external Hard Drives that came in touch with the computer and if you connect them (the external Hard drive and USB) to another computer and open one of the shortcut (malware-infected) files, you will infect that computer as well.
The best way to get rid of this infection is via Safe Mode (click here to learn how to boot into safe mode), while all the pieces of software are "asleep."
Once you are in Safe Mode, follow the steps below:
- Delete the antivirus (if) you had installed before and download one of the following utilities (up to you which one): Malwarebytes' Anti-Malware, Junkware Removal Tool, AdwCleaner;
- Install one of these three pieces of software (or another one) and run a Full/Deep scan, which you should NOT interrupt;
- Once the scan is completed, delete (quarantine) the viruses and restart the computer.
More infos
-
Avoid visiting suspicious websites
1(4)0(0)People are aware that there are many websites out there designed to steal their data; However, the hardest part is to identify those websites. Usually those websites offer paid versions of popular softwares (such as antiviruses, games etc.), or an easy way for making money without effort. Once you open the website you will be asked to install a piece of software that allegedly improves your browsing experience. Do not accept it because not only does it not improve your browsing experience, but also it infects your computer or mobile device.
If you are not sure whether a website is safe or not, you can check it with virustotal's engine. Virustotal is a website that provides free check-up for files and websites for viruses. It uses 55 different antivirus products and 61 online scan engines to check for viruses that the computer's antivirus may have missed.
All you need to do is to copy the link of the suspicious website in the designated field and wait for the results.
More infos
-
Check the application's permissions − Android
1(2)0(0)Check an application's permissions before installing it on your mobile device. If you notice something suspicious (i.e, a game requires access to your camera), don't install it.
Before you install an Android application via Google Play(store), you will be shown what permissions the application requires:
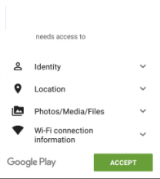
Note: You cannot change the application's permissions on an Android mobile device, however, you can check them so that you decide whether you will install a particular application or not (via Google Play Store).More infos Like Solutionbay?
Like Solutionbay?
Also check out our other projects :) See all projects -
Malwarebytes Anti−Malware (MBAM)
1(1)0(0)Malwarebytes Anti-Malware (MBAM) is a free computer virus removal tool (that offers a premium plan, too)More infos -
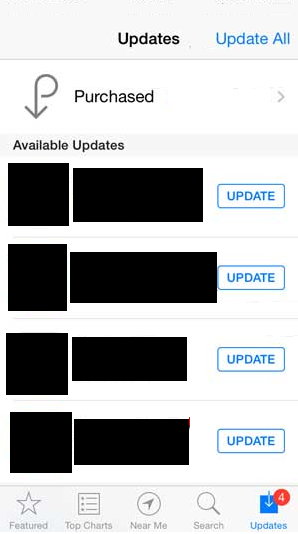
Update your device's operating system regularly
0(7)0(0)The number of threats to your computer and mobile device is increasing every day. Many developers work hard to find weak spots (bugs) in the operating systems and create new viruses so that they can steal personal data from millions of users.
To be on the safe side, and as a good mobile device/computer virus protection apply the recently released updates once you receive a notification that there is one. DO NOT DOWNLOAD UPDATES from third-party websites because they might have been modified to harm you.
To learn how to check for updates, and update your computer or mobile device's operating system, check out the don't know how to update my operating system solutions.
More infos
-
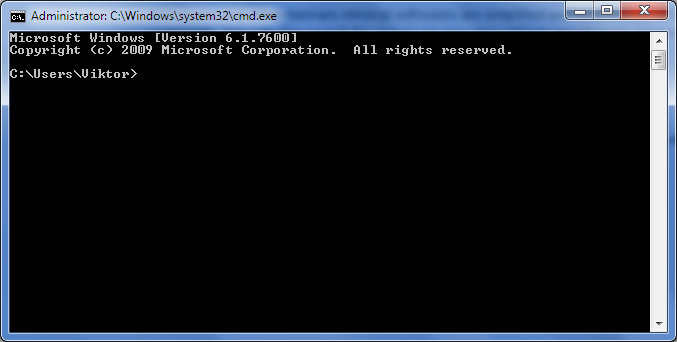
Scan for viruses in Safe Mode (Windows)
0(6)0(0)Viruses are designed to deprive you of the pleasure to browse the net and download files quickly and nowadays it is difficult to tell which is the worst computer virus. The solution is to remove them; however, there are some viruses which may incapacitate your antivirus and prevent it from operating normally. If you try reinstalling it or install a different one, the result will be the same.
If you wonder how to get rid of a virus on your computer, you need to access the safe mode (so that the virus remains inactive). If don't know how to get into Safe Mode, check the don't know how to boot in Safe Mode guide to find out.
Once you're in safe mode:
- Uninstall the previous antivirus (if any) from the Control panel. If you don't know how to uninstall it, check out the don't know how to uninstall a program/an application solutions.
- Download a fresh copy of an antivirus software and scan your computer. Since the virus (or viruses) is inactive, it will be easier for the antivirus to delete it.
*If you are not sure which antivirus software to download and install, check out the don't know which antivirus software to install solutions. - Run a full malware scan with Malwarebytes Anti-Malware followed by SFC /SCANNOW command in CMD (open the start menu and type cmd in the search box, right-click on it and Run as Administrator, and type SFC /SCANNOW in the window) to repair any system file damage the malware has done.
More infos
- Uninstall the previous antivirus (if any) from the Control panel. If you don't know how to uninstall it, check out the don't know how to uninstall a program/an application solutions.
-
Install Malwarebytes Anti−Malware
0(6)0(0) Malwarebytes Anti-Malware (MBAM) is a free computer virus removal tool (that offers a premium plan, too). It is an anti-malware software that scans for, identifies the symptoms of computer virus (or malicious software), and removes different types of malicious software (adware, spyware, trojans). Also, it offers an easy-to-use interface and a short wait time for scans.
Malwarebytes Anti-Malware (MBAM) is a free computer virus removal tool (that offers a premium plan, too). It is an anti-malware software that scans for, identifies the symptoms of computer virus (or malicious software), and removes different types of malicious software (adware, spyware, trojans). Also, it offers an easy-to-use interface and a short wait time for scans.Download it from the official website, install it on your computer, click of the Scan Now button and wait for the treats to be eliminated.
MBAM also has a premium version which offers a full-time background 'Malware Protection' and Malicious Website Protection, and a shorter wait time for scans, which is not the case with the free version.
Note: Although MBAM automatically updates its database, you can also check for updates manually by clicking Update. For best results, it is recommended to install it and scan for viruses with it while you are in safe mode. If you don't know how to enter the safe mode, click here to learn more.
More infos
-
Scan for and remove adwares
0(6)0(0)If you see annoying advertisements you cannot close, or get redirected to a different website without your consent, it's possible that your computer is infected with a malicious adware.
Adware is a term frequently used to describe a form of malware (malicious software) which presents unwanted advertisements when you browse the net. The advertisements produced by adware are sometimes in the form of a pop-up window titled "an offer you can't miss" or some similar phrazes. Those advertisements automatically open webpages infected with a malware (virus, worm, spyware and etc.) which invaded your computer without your knowledge.
If you wonder how to get rid of a virus on your computer, and of other types of malicious software, the best way to fight adwares (and other types of malicious software) is to install an antivirus, antispyware or an adware removal tool. Malwarebytes' Anti-Malware, (for Windows and Mac OS), SuperAntiSpyware (for Windows only) and BitDefender Adware Removal Tool (for Windows and Mac OS) are the most downloaded and trusted. Install them and run periodic scans. Also, be careful what web pages you visit and make sure to install software from trustworthy webpages only (Cnet, Filehippo etc.).
Note: If you are not sure which antivirus software to install, feel free to check the don't know which software to install solutions.
More infos Like Solutionbay?
Like Solutionbay?
Also check out our other projects :) See all projects -
Scan for and remove ransomwares
0(6)0(0)Considered to be the worst computer virus, ransomware is a type of malware that restricts the users' access to the computer and forces the users to pay a "ransom" to the operators of the malware in order to remove the restriction. Although very rare to get, it can sometimes cause data loss (you will have to reinstall Windows, and the "C:" drive will be wiped). It can also prevent you from accessing Windows, encrypt files so you can't use them, stop certain software from running (e.g the web browser) make you complete surveys and etc.
The best way to remove it, is by installing an anti-malware software such as Malwarebytes' Anti-Malware, through Safe Mode.
If you don't know how to get into safe mode, check out these solutions.
Note: If you already had an antivirus (anti-malware) installed, remove it in the control panel. If you don't know how to uninstall a program, check out these solutions.
Also, DO NOT PAY THE "FINE", Because there is no guarantee that the ransomware will be removed from your computer.
More infos
-
Keep the installed programs/applications up to date
0(6)0(0)Another way for a virus to infect your computer or mobile device is through an outdated software. Many people just install pieces of software, without checking for updates from time to time. An outdated software can be a way for hackers to gain access to your computer or mobile device as new types of computer virus are "born" on a daily basis.
To learn how to update the applications installed in your device, check out the don't know how to update programs/applications solutions
More infos
-
Disable the hide extensions for known file types option
0(6)0(0)The file extension (or file name extension) are the letters shown immediately after the last period of the file name (e.g software.EXE; picture.JPG). Many users think that JPG files, MP3 and other audio or visual file extensions cannot be hosts of viruses and open them without thinking. However, hackers take advantage of this fact and name their malicious files in a similar manner (e.g. picture.jpg) and count on the fact that Windows will not show the true file extension (the full name of the above-stated example would be picture.jpg.EXE)
Windows hides the file extensions by default (it hides .exe; .jpg and etc.) and the virus looks as a harmless file, but once you open it, it infects your computer.
The best way for you to be 100% sure about what you open (a picture, software and etc.), and "the best computer virus protection" is to see the file extensions.
To enable this option follow the steps below:
- Go to (My) Computer -> Click Tools (Press the ALT key on your keyboard if you don't see Tools) -> Select Folder Options
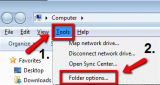
- Select the View tab -> Uncheck (Untick) the checkbox next to Hide extensions for known file types -> Apply the changes -> Press OK

Note: If you use Windows 10, click File and select Change folder and search options in order to access the Folder Options window
More infos
- Go to (My) Computer -> Click Tools (Press the ALT key on your keyboard if you don't see Tools) -> Select Folder Options
-
Take your computer/mobile device to a repair shop
0(6)0(0)If you cannot remove the viruses from your computer or mobile device by yourself, or you tried everything and nothing worked, and still wonder how to remove virus from computer or mobile device, take your computer or mobile device to an electronics repair store. They will take care for your computer or mobile device and remove every malware they detect.
More infos
-
Install SuperAntiSpyware
0(5)0(0)If you wonder how to detect spyware on computer (which is considered the most dangerous computer virus, by a group of users) and remove it, try installing SuperAntiSpyware. SuperAntiSpyware is one of the top tools for removing malware, viruses and other threats. It detects and removes different types of malware (such as Spyware, Adware, Trojans and etc.).
It doesn't ask for a lot of resources from your computer (it won't slow it down), and it won't cause you trouble if you have already installed another antispyware or antivirus.
Download it from the official website, install it, click on Scan this computer and scan your computer from time to time.
Note: To unlock all the features SuperAntiSpyware has, install the full version (i.e. the Professional Edition).
More infos Like Solutionbay?
Like Solutionbay?
Also check out our other projects :) See all projects -
Scan for and remove spywares
0(5)0(0)To define computer spyware: it is a piece of software designed to steal personal data (especially credit card numbers, account passwords etc.), without your knowledge.
How do you get spyware on your computer? There are many ways for spywares to invade your computer, such as: visiting websites like "Enter our site and win an Iphone" or "Click here to download ..."(any software which is not free). This means that spywares are harmful only if you have access to the internet. Once they invade your computer they store everything you write and periodically send it to the creator of the spyware who most often "unloads" your credit card.
How to detect spyware on computer? The best way to detect and fight against them is to install an antivirus, antimalware or an antispyware software. Malwarebytes' Anti-Malware (for Windows and Mac OS) and SuperAntiSpyware (for Windows only) are known to protect many computers from being invaded by spywares. Install one of them and run periodic scans.
Note: If you use a computer and you have sensitive data stored on it, it would be better to buy the full version of one of these softwares (also called Internet security). It will run full scans in the background and the wait time will be shorter.
More infos
-
Scan for keyloggers
0(5)0(0)Keyloggers are designed to record every single letter you write on your keyboard. They are mostly used to steal personal data (credit card numbers, passwords) because they consume minimum resources and are hardly noticed by users. But, some people use them to control what their children do when they use the computer.
Although they share common traits with spywares (they both spy on the user's activity), they can be accessed by the user (if he manages to guess the secret combination, e.g. Ctrl + Shift + 1) and reprogrammed (change the location where the keylogger files are stored, change the email to which keylogger files are sent and etc.). Unless you have an access to the net, you cannot be harmed by keyloggers.
The best way to fight them is to install an antivirus or an antispyware software. Malwarebytes' Anti-Malware (a free computer virus removal tool, with an option for premium features) is one of the best options to fight keyloggers. Also, scan your computer more often and AVOID VISITING SUSPICIOUS PAGES, which is the best computer virus protection.
Note: If you want to use a keylogger to watch over your child(ren), download it from trustworthy sites only (e.g. Cnet), because you risk becoming someone else's "child" without your knowledge.
More infos
-
Scan for and remove zombie/bot malware infections
0(5)0(0)A botnet is a network consisting of hacked computers that are infected by malware and controlled by the botnet owner without the computer owner’s consent and knowledge.
The bots can be used to launch DDoS attacks that can cause a website to go offline, send spam messages, drive fake traffic, click advertisements and much more, depending on the botnet owner. Normally the user won’t even notice that their computer is a zombie bot being controlled because the malware is programmed to stay hidden as long as possible, by bypassing both known antivirus or firewall software and does not damage nor change any part of the operating system that may trigger the owner’s suspicion.
The best way to remove a Zombie/Bot malware infection is through Safe Mode. To get into Safe Mode:
- If you use Windows versions other than Windows 8(.1)/10: Restart your computer and press F8 (or F12) before the Windows logo appears;
*If you use Windows 8(.1)/10: hold the SHIFT key and click Restart at the login screen. - Once the Advanced boot screen appears highlight Safe mode with Networking out of the offered options and press Enter on your keyboard (if you are not sure how, read this);
- After that, install a fresh copy of an antimalware, antivirus, bot-removal tools. Very famous tools include: Malwarebytes' Anti-Malware , RuBotted, Mirage Anti-Bot, Norton Power Eraser;
- Scan your computer and after the scan is completed and the bot removed, restart the computer. Repeat this procedure from time to time, and avoid visiting suspicious websites.
Remember: The answer to the "how to protect computer from virus" question is not visiting suspicious websites at all.
More infos
- If you use Windows versions other than Windows 8(.1)/10: Restart your computer and press F8 (or F12) before the Windows logo appears;
-
Scan pieces of software and URLs using VirusTotal.com
0(5)0(0)VirusTotal is a website that provides free check-up for files and websites for viruses. It uses 55 different antivirus products and 61 online scan engines to check for viruses that the computer's or the mobile device's antivirus may have missed. This is a good way to prevent malwares from invading your computer and an answer to the "how to get rid of a computer virus (or of a mobile device one)" question.
Upload a file (up to 128 MB) or copy a URL you find suspicious. Based on analyses of all the softwares you will be informed whether the file or the URL is malicious and spare you from troubles.
Note: There are some files which may be recognised as viruses by SOME of the antiviruses, and they are actually not. Those files are known as false positives. So if a file is treated as a virus by small number of antiviruses (e.g 2 out of 10), then it is most likely a false positive file.
More infos
-
Monitor your computer with WinPatrol
0(5)0(0)If you wonder how to check computer for viruses and protect it, the best way is to prevent malicious software from invading your computer in the first place. WinPatrol is a very popular software which scans for the symptoms of computer virus and alerts you in case of hijackings, malware attacks and changes made to your computer, without your permission (and it also includes other useful utilities which enhance your system's performance).
While traditional security programs scan your hard drive searching for previously identified threats, WinPatrol takes screenshot of your critical system resources and alerts you if any changes occur without your knowledge. You'll be able to remove dangerous new programs while others prepare to update their definition/signature data files.
Download it from the official website only, install it and follow the instructions.
More infos Like Solutionbay?
Like Solutionbay?
Also check out our other projects :) See all projects -
Avoid opening suspicious emails
0(5)0(0)Phishing email messages, links, or phone calls are another way for a virus to find its way to your computer. You are asked to provide your credit card number, log in to Facebook (or other social network) through the email and etc.
The best way to protect yourself from phishing emails, and the best mobile device or computer virus protection in general, is to avoid opening them and READ THE TITLE CAREFULLY. So, if you notice an email that has a suspicious title and is sent from a suspicious email address, don't open it. Usually suspicious mails are directed to the Junk folder and valid emails are shown in the regular Inbox folder. However, there are some cases where valid emails are shown in the junk folder.
Also, ignore emails that inform you that you've won a contest or emails from a stranger asking for assistance with their inheritance.
Note: If you are not sure how to recognise a phishing email, read this tutorial. If you are still not able to recognise a phishing email, consider installing an antivirus software which will delete phishing emails automatically.
If you are not sure which antivirus software to install, check out the don't know which antivirus software to install solutions.
More infos
-
Use a Firewall
0(5)0(0)If you wonder how to protect computer from virus, you may take advantage of the Firewall. The OS (Operating System) Firewall is designed to protect you from the attacks of hackers. It can also stop your computer from sending malicious software to other computers. That is why, it is very important to have it activated all the time. By activating the firewall you will minimize the chances for hackers to find a bug in your computer.
To activate it:
- Windows:
Start -> Control Panel -> Windows Firewall (or type 'Firewall' in the search box) -> click Turn Windows Firewall on or off in the left pane -> Click Turn on Windows Firewall under each network location that you want to help protect, and apply the changes.
- MacOS:
- Os X v10.5
Apple menu -> System Preferences -> Security -> Firewall -> Choose what mode you would like the Firewall to use
- OS X v10.6 and later
Apple menu -> System Preferences -> Security (or Security & Privacy) -> Click the Firewall tab -> Unlock the pane by clicking the lock in the lower-left corner and enter the administrator username and password -> Turn On Firewall (or Start) -> Click Advanced to customize the firewall configuration
Note: Some antiviruses have their own Firewall that will substitute the default Windows Firewall once they are installed (You will be notified by the Antivirus software). Do not enable the default Windows Firewall in those situations.
More infos
-
Install mobile applications from Google Play(store) only
0(5)0(0) Google Play (store) is the safest database for Android applications. Every application undergoes various tests (stability, security) before it is offered to the end-users.
Google Play (store) is the safest database for Android applications. Every application undergoes various tests (stability, security) before it is offered to the end-users. That is why you should always download and install Play-store-approved applications only.
To download applications from Google Play, tap on Google Play (Store) and search for the application you want to install.
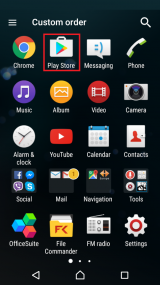
Note: Avoid installing applications that are not from Google Play store (especially cracked, full-version applications) because you may become a victim of hackers, and have your sensitive data stolen.
More infos
-
Install mobile applications from App store only
0(5)0(0) Apple's App Store is the safest database for iOS mobile applications. Every application undergoes various tests (stability, security) before it is offered to the end users.
Apple's App Store is the safest database for iOS mobile applications. Every application undergoes various tests (stability, security) before it is offered to the end users. In the mobile device menu, tap App Store and search for the application you want to install.
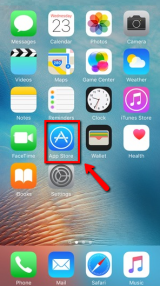
Note: Avoid installing applications that are not from App store (especially Cracked Full version applications) because you may become a victim of hackers, and have your sensitive data stolen.
More infos
-
Install Junkware Removal Tool
0(4)0(0)The question does my computer have malware is sometimes difficult to answer, because malwares are available in all shapes and sizes. Junkware Removal Tool is a utility that searches for and removes common adwares, toolbars, and potentially unwanted programs (PUPs) from your computer. A common tactic among freeware publishers is to offer their products for free, but "equip" them with PUPs in order to earn revenue. This tool will help you remove these types of programs.
Click here to download it and once you've had it downloaded, install it.
Once you run the Junkware Removal Tool, it will scan your computer and remove every trace of these programs including their files, registry keys, and folders stored in your computer quickly and efficiently.
More infos Like Solutionbay?
Like Solutionbay?
Also check out our other projects :) See all projects -
Avoid suspicious ads (advertisements) on websites
0(4)0(0)If you wonder how to protect computer from virus or how to protect your mobile device, you should avoid clicking on suspicious ads. Unfortunately, they are on every second website you visit, waiting for you to click them. They offer you money, free mobile devices (usually iPhones), vacations and countless stuff. But the only thing you actually get for free is a malware, and an empty credit card.
The best way to protect yourself from ads is to avoid opening them. Remember that there is no such thing as free lunch. Also, consider installing a good antivirus software that will protect you from suspicious ads.
If you aren't sure which antivirus software to install, check out the don't know which antivirus software to install solutions.
More infos
-
Remove the (browser) hijacker
0(4)0(0)Does my computer have malware? Sometimes, this question is difficult to answer because there are different types of malware (some easily noticeable, others not). Browser hijacker is a type of malware that alters the search and error page of web browser and redirects the user to a page set by the developer of the hijacker (which is often malicious). Browser hijacker is created for a number of reasons among which your personal data (Credit card number). A computer can get affected with browser hijacker virus through a software, e-mail and etc.
Your computer is infected with hijacker if:
- The Default search engine (Google, Yahoo, Bing) of your browser alters without your permission
- The default home page of your browser is not the one you've set as default (e.g. Google, Yahoo, Bing or other)
- You are flooded with advertisements
- You are automatically directed to another webpage you had no intention to visit (e.g. you want to open facebook.com, but you end up being redirected to anywebpage.com)
Removing it in the Control Panel (Start -> Control Panel -> Programs and Features/Uninstall a program) is a temporary solution because once you restart your browser (or computer) everything will be the same.
How to clean computer from malware, including hijackers? You can remove hijackers using Malwarebytes' Anti-Malware, which is one of the best for the task. Enter the Safe Mode and run a full scan of your computer. To get into the safe mode:
Windows:- If you use Windows versions other than Windows 8(.1)/10: Restart your computer and press F8 (or F12) before the Windows logo appears
- If you use Windows 8(.1)/10: hold the SHIFT key and click Restart at the login screen
Once the Advanced boot screen appears, highlight Safe mode with Networking out of the offered options and press Enter on your keyboard.
Mac OS:- Turn on your computer and press and hold the Shift key until you see the Apple logo and a small progress bar
After you enter the safe mode, install Malwarebytes and run a full scan. Once the scan is completed, and the hijacker deleted, restart your computer.
Note: If you are not sure how to access the safe mode, check the don't know how to boot in Safe Mode guide.
More infos
-
Install Norton Power Eraser
0(3)0(0)Norton Power Eraser is a good computer virus cleaner, designed to eliminate deeply embedded and difficult-to-remove crimeware that traditional virus scanning doesn't always detect. It targets "stubborn" files that usually reinfect your computer after reboot and forcibly removes them. Because it cleans aggressively, it can delete critical system files, so it must be used with care.
Download it from the official website.
Note: Due to its radical approach, it is recommended to install it as a last option.
More infos
-
Install AdwCleaner
0(3)0(0)AdwCleaner is a program that scans for and deletes Adwares, Toolbars and other Potentially Unwanted Programs (PUPs) from your computer. By using AdwCleaner you can easily remove many of these types of malware and have a better user experience on your computer while browsing the web.
The types of programs that AdwCleaner targets are usually free programs that you download from the net. These programs are usually installed along with the program you downloaded. Unless you perform a Custom install, these unwanted programs will automatically be installed on your computer leaving you with extra browser toolbars, adware, and other unwanted programs. AdwCleaner is designed to prevent this.
Click here to download it for free.
Using AdwCleaner is very simple:
- Download the program and run it
- You will then be presented with a screen that contains a Scan and Clean button. Click the Scan button to scan your computer for unwanted programs and then display all the files, folders, and registry entries found on your computer that are used by adware programs.
- Once the scan is completed, look through the scan results and uncheck any entries you have no desire to remove.
- Then, click the Clean button, which will cause AdwCleaner to reboot your computer and remove the files and registry entries associated with the various adware that you are removing.
- After the removal process is completed, AdwCleaner will display a log showing the files, folders, and registry entries that were removed on the next startup.
More infos
-
Install USB Disk Security
0(3)0(0)USB Disk Security is a good software which blocks threats that can inflict damage on your computer or your personal data via USBs or external hard drives, without allowing the malicious software to infiltrate in your computer and is an answer to the frequently asked question "how to clean computer from malware?". It plays the role of a filter that detects and deletes infections on USBs and external hard drives. It runs in the background without consuming too much of your computer's RAM memory.
Download it from the official website, install it and let it run in the background and every time you plug in a USB drive in your computer, a window pops up and scans the USB. If it detects a virus on it, click Delete/Delete all (follow the on-screen instructions) and re-insert the USB.
More infos Like Solutionbay?
Like Solutionbay?
Also check out our other projects :) See all projects -
Remove third−party browser extensions (toolbars)
0(3)0(0)A browser toolbar is usually a horizontal line with shortcut icons on it that resides within a browser's window. Its primary purpose is to provide a better user experience. However, some toolbars can be harmful. Almost every computer user has come across browser toolbars that he/she didn't (want to) install showing up on the screen. They usually get installed when you install a piece of software, without your awareness or consent, and certain toolbars can make way for a virus in your computer, by redirecting you to a malicious website automatically.
To learn how to remove browser extensions, check out the don't know how to remove browser extensions solutions
More infos
-
Remove third−party browser toolbars via control panel
0(3)0(0)A browser toolbar is usually a horizontal line with shortcut icons on it that resides within a browser's window. Its primary purpose is to provide a better user experience. However, sometimes it can be harmful. Almost every computer user has come across browser toolbars that he/she didn't want to install. They usually get installed when you install a software, without your awareness or consent, and can make way for a virus in your computer, by opening a malicious website automatically.
You can remove most of the toolbars from Control Panel:
Start -> Control Panel -> Programs and Features/Uninstall a program
To prevent toolbars from installing, always select (check) the Advanced settings (or Custom Installation) field that every software installer offers and untick "Install XYZ toolbar", and/or Make XYZ the default webpage.
Note: There are some browser toolbars that can only be removed in the web browser (check out the don't know how to remove browser extensions guide to learn how to remove them) and others for which you may need the assistance of a computer virus cleaner.
More infos
-
Scan for backdoor trojans
0(3)0(0)A Backdoor Trojan is a malicious software that usually finds a way into its victim's computers without their knowledge or consent, through websites, software and etc. It allows the software developer that created it to control the computer of the victim and steal sensitive data.
To delete a Backdoor Trojan, and every trojan computer virus, you need an antivirus software and free time. Malwarebytes' Anti-Malware is one of the best for the task. The best way to remove a Backdoor Trojan is through safe mode:
Boot your computer in safe mode and once it is in safe mode, install a fresh copy of Malwarebytes Anti-Malware (or other antivirus software) and run a FULL scan, to ensure that everything is scanned thoroughly. Once the Trojan is deleted, restart your computer.
Note: If you are not sure how to enter the safe mode, feel free to consult the don't know how to boot in Safe Mode guide.
More infos
-
Back up your data
0(3)0(0)If your computer or mobile device is attacked by a virus, it may suffer a severe data loss. A good precaution against data loss includes making data backup.
Buy an external hard drive and copy important data on it. Use it on a virus-free computer only, to avoid infecting the back-up data. Every OS (operating system) offers a data-backup option.
To learn how to back up your data, check out the don't know how to back up my files solutions.
More infos
-
Avoid web pop−ups that inform you that your computer is infected
0(3)0(0)If you are browsing the net and a pop-up that warns you about the condition of your computer appears, close it immediately. If you click on it, it will allegedly scan your computer and later it will ask you to install a piece of software that will "improve" your computer's stability (eventually it will, but with a virus).
Also, ignore and close pop-ups that pretend to be a Windows alert (the ones which use the Windows theme).
If the pop-up appears only when you visit a specific website, avoid that website. However, if it appears on every website you visit, then your computer might already be infected.
To clean it, you need to install an antivirus software. If you aren't sure which antivirus software to install, check out the don't know which antivirus software to install solutions.
More infos Like Solutionbay?
Like Solutionbay?
Also check out our other projects :) See all projects -
Ensure to untick unwanted checkboxes during software installation
0(2)0(0)Most people don't even pay attention to the options a program installer offers. They just hit the install button and wait for the installation to be completed. What they don't know is that toolbars and other unwanted programs are most often installed along with the desired softwares people download from the Internet.
To prevent toolbars and other unwanted software from installing, select the Advanced/Custom settings field that every software installer offers and untick Install XYZ toolbar, and/or Make XYZ the default webpage.
More infos
-
Install an antivirus software
0(2)0(0)If you wonder how to get rid of a computer virus, or a virus on your mobile device, the answer is simple - install an antivirus. A good antivirus software is essential, if you want to keep your personal data and files (pictures, videos, documents, etc.) to yourself. If you don't have an antivirus software installed, make sure to install one as quick as possible.
If you are not sure which antivirus software to install, check out the don't know which antivirus software to install solutions.
More infos
-
Install Malwarebytes' Mobile Security
0(1)0(0)If you use a mobile device, you can download Malwarebytes Anti-Malware for free, from Google Play (Android) and App Store (iOS). Once you install it in your mobile device, run periodic scans to keep your data safe.
More infos
-
Read the End User License Agreement (EULA)
0(1)0(0)Before you install a piece of software, be sure to read the End User License Agreement, or EULA. It contains information on how this software interacts with your computer (or mobile device) and use your private information. If you find that a particular software is using your personal data or tracking your computer (or mobile device), then it is up to you to determine whether you really want to install the software.
More infos
-
Delete text messages from unknown senders that include a link
0(1)0(0)If you receive one of those messages that ask for your personal data or ask you to download and install an application, and it includes link where you can enter your data, the best thing to do is to DELETE it. This is just an another trick of hackers to infect your mobile device and steal your personal data.
More infos Like Solutionbay?
Like Solutionbay?
Also check out our other projects :) See all projects -
Scan for and remove viruses via CMD (command prompt)
0(0)0(0)Antiviruses and other malware removal softwares are simplified and easy-to-use softwares that detect and delete viruses through commands. You can also search for viruses on your own without installing an antivirus software. All you have to do is to run CMD (Command Prompt).
To access the CMD:
Start menu -> Type CMD in the start-menu search box -> Right-click it and select Run as Administrator -> follow these instructions to the last letter


 More infos
More infos
-
Scan for viruses in Safe Mode / Safe Boot (Mac)
0(0)0(0)Viruses are designed to deprive you of the pleasure to browse the net and download files quickly. The solution is to remove them; however, there are some viruses which may incapacitate your antivirus and prevent it from operating normally. If you try reinstalling it or install a different one, the result will be the same.
In a situation like this, you need to access the safe mode or safe boot (so that the virus remains inactive). If you are not sure how to get into safe mode, click don't know how to boot in Safe Mode guide.
Once you are in safe mode, download a fresh copy of an antivirus software and scan your computer. Since the virus (or viruses) is inactive it will be easier for the antivirus to delete it (them). Also, you can run a full malware scan with Malwarebytes' Anti-Malware to make sure that the virus(es) is(are) removed.
Note: If you are not sure which antivirus software to download and install, check out the don't know which antivirus software to install.
More infos
-
Check the application's permissions − iOS
0(0)0(0)Check an application's permissions before and after installing it on your mobile device. If you notice something suspicious (i.e a game requires access to your camera), don't install the application.
To check the permissions an application has:
Go to Settings -> Scroll down to the list of installed applications in your device and select an application -> Change permissions by moving the slider to the left of right (e.g. if you don't want an application to have access to your microphone - move the slider to the left, and vice versa).
 More infos
More infos
Login to Solutionbay
Join Solutionbay
Please click on the confirmation link we just sent you to
If you don’t receive the email in the next 2 minutes please check your junk folder, and add [email protected] to your safe sender list.
